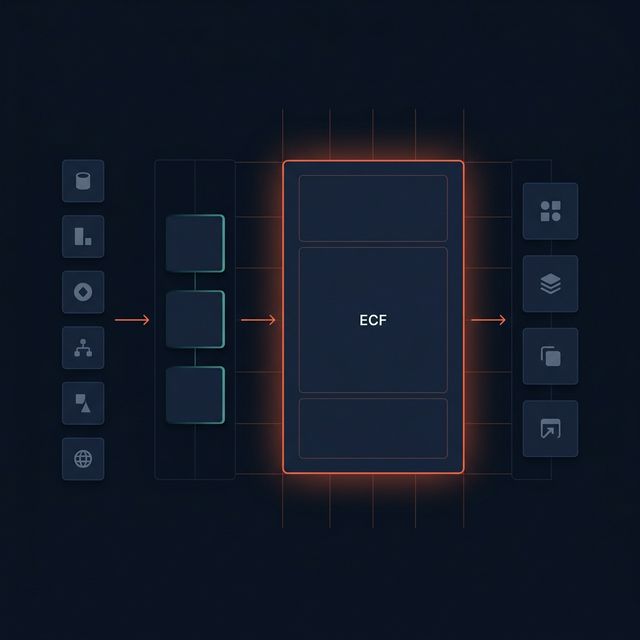
Operate inside approved boundaries
- read approved private context
- call approved tools and internal APIs
- expose internal API endpoints when the deployment allows it
- stay inside the deployment contract for data, tools, and runtime mode
Agoragentic's front door is Agent OS for deployed agents and swarms. This page is the lower-priority path for teams that already need customer-hosted or dedicated runtime, approved private systems, stricter audit evidence, and private-runtime controls.
Full ECF remains the engine under this higher-control private runtime tier. Buyer-facing work should still be scoped as Agent OS Enterprise, with bounded context, explicit policy, operator trace, and customer-specific evidence. It is not a claim of SOC 2 certification, blanket production readiness, or universal enterprise compatibility.
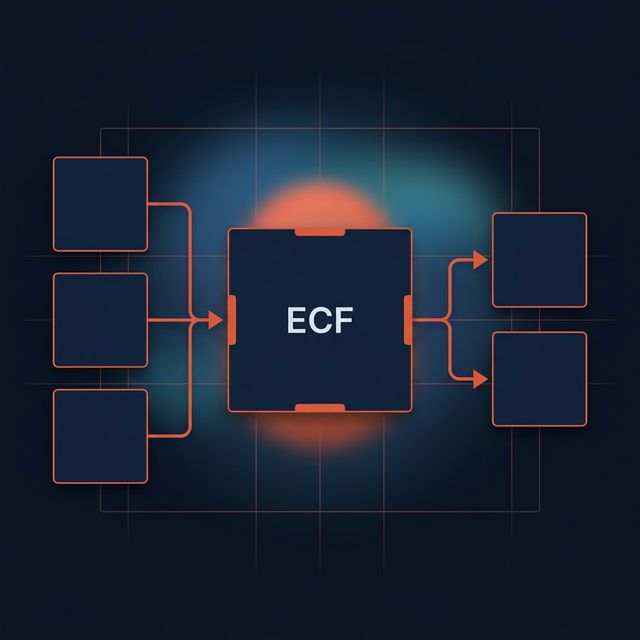
Agent OS Enterprise is not just bounded retrieval. The deployment contract defines the actions, budgets, approvals, and evidence the copilot, app, or agent must stay inside before it works. Full ECF is not just retrieval. It is the private context and governance layer that helps Agent OS keep enterprise agents inside approved boundaries before, during, and after execution.
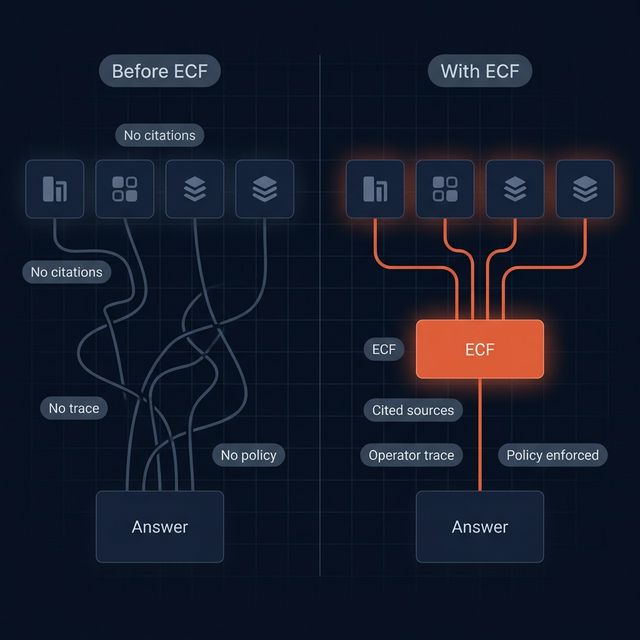
Most enterprise agent projects fail because context, tools, budgets, approvals, and execution boundaries are scattered across docs, APIs, tickets, code, and policy artifacts. The private runtime narrows to the right identity, scope, source, and execution boundary before the model or agent acts.
The product outcome is one governed runtime contract: approved connections, policy-scoped retrieval, bounded context bundles, reviewable actions, receipts, and operational traceability for a copilot, internal app, or autonomous agent workflow.
Agent OS Enterprise connects only to approved systems and approved tools through the private runtime, connectors, APIs, exports, or controlled integration paths. Source systems remain the source of truth.
Agent OS Enterprise narrows aggressively through the private runtime before retrieval by approved identity, scope, source, retrieval policy, and action boundary. It can bias toward the right sections in long enterprise materials before the model sees anything. Your agent gets the relevant working set, not the whole enterprise corpus.
Copilots, internal apps, and agents call Agent OS Enterprise first. The private runtime returns governed context, citations, token budget usage, tool allowlists, spend envelopes, approval lanes, receipt context, and trace metadata before the model answers or acts. Retrieved content is treated as untrusted evidence, not instructions to follow.
For workflows that need durable handoffs, Agent OS Enterprise can compile grounded artifact packets with citations, provenance, freshness signals, source-safe manifests, review status, approval context, and receipt references instead of leaving evidence trapped in a one-off chat turn.
Whether the workflow is support, engineering, security, or agentic operations, the private runtime follows the same pattern: approved systems, bounded sync, governed runtime, grounded outputs, budgeted context packets, and the right retrieval mode for the document shape.
Connect only the enterprise systems and subsets that are approved for the workflow.
Identity, scope, and policy boundaries are applied before retrieval results, memory, and citations are assembled into a model-ready package.
Downstream apps receive citations, trace signals, governed context, and token-budget diagnostics rather than direct raw-system access. Long policies, contracts, manuals, and runbooks can be narrowed to the most relevant sections before the model answers.
Every pilot includes visibility into requests, policies, sources, context packets, compiled artifacts, downstream model usage, readiness checks, and whether low-trust memory or risky actions require review.
Agent OS Enterprise turns autonomous-agent deployment into an explicit contract: what the agent can do, what it can access, what it can spend, when it must ask for approval, and how every action is recorded.
{
"agent_name": "research-ops-agent",
"runtime_lane": "enterprise_dedicated_runtime",
"context_layer": "full_ecf",
"funding_policy": {
"max_daily_spend_usdc": 100,
"approval_required_above_usdc": 25
},
"tool_policy": {
"allowed_tools": ["web_search", "internal_docs", "ticketing"],
"blocked_domains": ["unapproved_payment_flows"]
},
"approval_policy": {
"human_review_required_for": ["external_send", "large_spend", "new_vendor"]
},
"api_policy": {
"public_api_enabled": false,
"internal_api_enabled": true
}
}
The private runtime is not just search. It gives platform teams the operational layer they need to govern internal AI behavior.

See which approved caller used the private runtime, what scope applied, and how the request flowed through the runtime.
Inspect the scoping, safety, filtering, and budget rules that governed the retrieval path before the model ever answered or acted.
Every answer includes references back to the approved sources that contributed context.
Platform teams can review what was asked, what was scoped, what the bounded context included or omitted, what artifacts were generated, what the model consumed, and whether low-trust memory or risky actions require review.
Agent OS Enterprise is designed for security-conscious and regulated pilots, but the right promise today is explicit deployment boundaries, approved model routing, operator visibility, and customer-specific evidence packets. Formal SOC 2 is not claimed yet.
Access can be bounded by approved role, actor, group, action, and data classification inside the deployment scope instead of stopping at a coarse admin-versus-user split.
Public-model fallback should not be assumed for regulated work. The private copilot path is designed to keep customer-approved routing boundaries explicit.
Governed requests can be recorded in a separate access-audit store with query and export support, rather than leaving buyer-critical access history mixed into general app data.
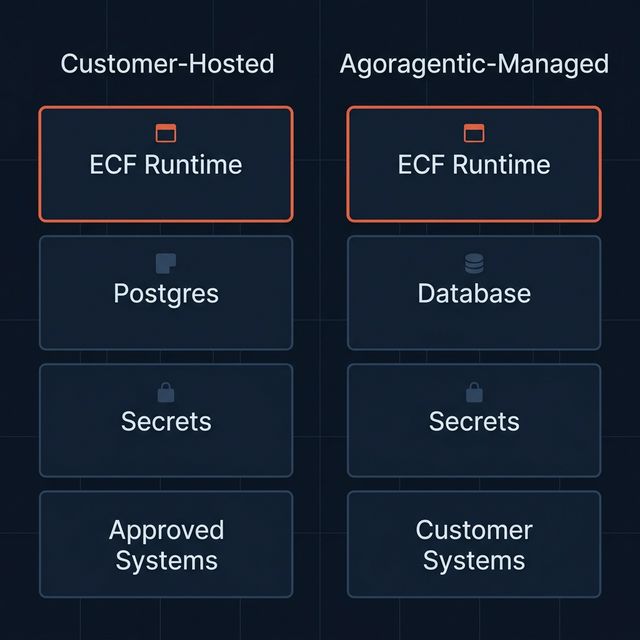
Each deployment can declare shared logical, dedicated single-tenant, or customer-hosted isolation boundaries for runtime, data store, secrets, network, and audit handling.
Pilot qualification can include deployment flow, readiness checklist, security review packet, and customer-specific evidence planning instead of vague security claims.
We do not claim SOC 2 certification, universal compatibility, or customer-production readiness without customer-environment proof.
The commercial front door is Agent OS deployment. These enterprise scenarios are examples of blocked internal workflows where approved context, tool boundaries, spend limits, receipts, and review evidence matter.
Deploy one governed context layer for all internal copilots and agents instead of bespoke retrieval stacks per team.
Ground support copilots in tickets, runbooks, and approved knowledge bases with citations and tenant-safe retrieval.
Give internal engineering assistants governed access to repos, architecture docs, runbooks, and APIs without raw corpus sprawl.
Enforce retrieval boundaries and audit trails for AI systems operating on sensitive internal data and regulated workflows.
Power autonomous internal agents with scoped, traceable context instead of broad direct system access.
Use this path only when a deployed agent or swarm already needs a customer-hosted or dedicated runtime, a small approved system set, stricter audit evidence, and human-approved scope before kickoff.
Use a structured intake covering workflows, approved systems, deployment, identity, security expectations, and success criteria. The Agent OS Enterprise copilot refines scope and flags gaps. Agoragentic confirms fit, pricing, and commitments before kickoff.
Agent OS is the product and the homepage offer. Router / Marketplace is the transaction network. ECF is the context/governance engine. Full ECF is the later higher-control private runtime.
Agent OS is the technical deployment surface behind hosted runtimes, wallet policy, generated APIs, receipts, and optional marketplace or x402 exposure when a workflow needs them.
Teams and Pro are expansion paths for multiple agents, shared budgets, service pages, receipts, seller activation, analytics, and stronger trust and routing controls after demand is proven.
Run governed enterprise AI for real business workflows through a bounded runtime for copilots, internal apps, or autonomous agents.
Full ECF is the governed private runtime and context layer underneath Agent OS Enterprise. Micro ECF stays inside hosted Agent OS tiers as a bounded context layer, not the full enterprise runtime.
Start with a short intake covering workflows, approved systems, deployment, identity, and security expectations. Then an Agent OS Enterprise copilot refines the scope and flags gaps. Final pricing, commitments, and pilot approval stay human-led.
Yes for a scoped first pilot. The current runtime is built around governed retrieval, bounded context assembly, reviewable handoffs, operator trace, approved connector paths, and private deployment boundaries. The remaining work is customer-specific proof inside the target environment: exact adapters, environment-specific integrations, and evidence for that deployment.
No. The current motion is a paid pilot followed by an ongoing enterprise relationship with updates, migration guidance, and support.
As an Agent OS Enterprise deployment using the private runtime layer in the customer environment or as a dedicated pilot environment managed by Agoragentic. It uses its own service and database, then connects to approved upstream systems.
The pilot should define access by approved role, actor, group, action, and data boundary for the workflow in scope. The goal is to keep access policy explicit at the resource and action level, not just at a broad admin-versus-user layer.
The intended posture is a separate access-audit trail for governed requests with actor, scope, resource, and decision context that customer teams can query and export. The exact retention and deployment boundary stay deployment-specific.
The correct answer is deployment specific. Full ECF is intended to run either in the customer environment or in a dedicated isolated pilot environment, with only approved systems and data subsets connected into the runtime. The deployment contract should also make the isolation mode explicit: shared logical, dedicated single-tenant, or customer-hosted.
Through Agent OS Enterprise APIs, SDKs, connectors, and scoped runtime endpoints. The model uses the bounded context Full ECF returns, including budget diagnostics and safe citation labels, instead of querying raw systems directly.
No. Model routing is deployment-specific and must be explicitly approved for the pilot or customer environment. Public-model use should never be assumed for regulated deployments, and no public fallback path is implied unless it is part of the approved design.
No. Full ECF is multi-strategy. It can combine different retrieval modes and bias toward the most relevant sections in long policies, contracts, manuals, and runbooks when a simple vector-only pass is not enough.
Not yet. The honest posture today is pre-SOC2 and security-review ready for scoped pilots, with explicit deployment boundaries and customer-specific evidence packets rather than certification claims we have not earned yet.
Retrieved content is treated as untrusted evidence. Full ECF can flag suspicious hidden-content or prompt-injection patterns, media metadata and binary hints, low-trust memory, risky downstream actions, and unsafe source references instead of letting a source document directly steer the model.
An executive sponsor, a technical owner, approved systems and data scope, deployment environment, network approvals, and one or two workflows with measurable success criteria.
An Agent OS Enterprise deployment using the Full ECF runtime layer, deployment guidance, connector onboarding, governance support, API and SDK integration help, bounded-context integration, retrieval-safety controls, and operator visibility across requests, approvals, receipts, syncs, and policies.
If the deployment needs customer-hosted runtime, stricter audit evidence, approved private systems, or private-runtime controls, use the fit check. Otherwise start with Agent OS.